How many letters are there in the alphabet? What is the name of the seventh letter? What are alphabetic numbers? Are you interested too? Going deeper!
Letters – antediluvian graphic signs for the designation of sounds in writing – are suitable not only for writing school essays, scientific reports or SMS-like “buy a beer, but I’ll also be there soon.” In addition, letters are great material for creating ciphers, passwords, games, and puzzles. A random letter generator is a tool for automatic selection of letters or sequences and/or a list/set of random letters in many languages: English, French, German, Spanish, Chinese, and dozens of others. A random letter generator can be used for a variety of purposes. It is surprisingly simple and easy to use – even a child can figure out the algorithm.
Random letter generators – what are they for?
A random letter generator is useful if you are:
- Teaching a child or expatriate the alphabet.
- Learning a foreign (and, in severe cases, your native) language.
- Coming up with a fun puzzle.
- Creating an equally unique nickname.
- Providing access to corporate programs.
- Developing board games.
- Writing texts, advertising, etc.
- Other (the most interesting are always hidden behind this word).
English letters
Tools usually display English letters by default. With their help, you can easily teach a kid or a foreign student the English alphabet. And you can quickly check how well the students have memorized your lessons.
French, German, and Spanish letters
The letters of the French, German, and Spanish alphabets are similar to the English ones. But there are more of them (who knows why?). According to the assignment, they will also be displayed in random order.
Greek and Hebrew letters
Another story is that these languages have fewer letters than English. Regardless of the quantity, the system will generate a random selection and instantly display the result.
Hieroglyphs and Slavic letters
Furthermore, the system will generate random Russian and Armenian letters. As well as Japanese (hiragana) and Chinese (over 3,000) characters. Whether the generator will simplify learning languages and practicing writing skills is another question. But you will find a beautiful ideogram for your desktop.
Is there a practical use for a random letter generator? Let’s look at a few examples:
Development of writing skills
Has the muse left you? We activate writing talent using the program. For example, let’s generate 10 random letters. Then, capitalize these letters in the first ten sentences of one story. Finally, create an interesting post for your social media profile – hello, glory!
Vocabulary boost
When learning a new language, a random letter generator will help you pump your vocabulary to the maximum. First, write as many words as possible, starting with the dropped letter. Made? Now write the words that end with it. Nothing complicated, right?
Word games
Generate 5–10 letters (the number is at your discretion) and arrange the quest. Then, go to work – look around and try to find words that begin with the letters that have fallen out. How many crows were counted along the way? And at work?
Turn on your imagination and use any of the top 5 random letter generators. Identify your favorite.
Random Letter Generator
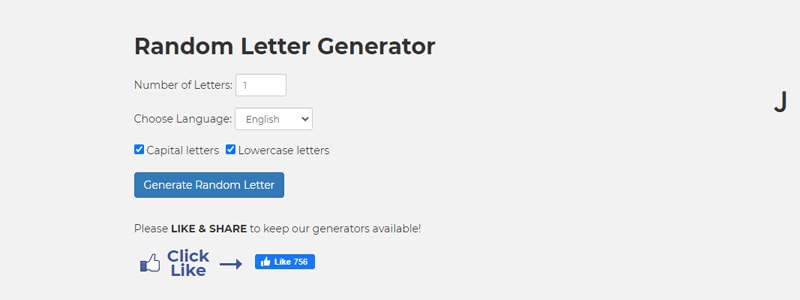
This random letter generator has a simple, intuitive interface: a generation field, text prompts, ad blocks (where would we be without them?). To get the result, you need to perform a few simple steps.
- Enter in the corresponding field the number of letters you want.
- Select the desired language.
- Press the “Create the random letter” button.
Supports ten languages and creates uppercase and lowercase letters. The generator also offers to use the functions of creating random numbers, words, nouns, synonyms, verbs, proper names, adjectives, whole random sentences, and phrases. And that’s not all: random Bible quotes, wedding hashtags, dinner ideas, motivational quotes, facts, questions, passwords, and assorted hints. Including tossing coins or dice. Impressive? Generates quickly. And free (as evidenced by the incredible amount of pop-up ads that inhibit creative work).
Letter Picker Wheel
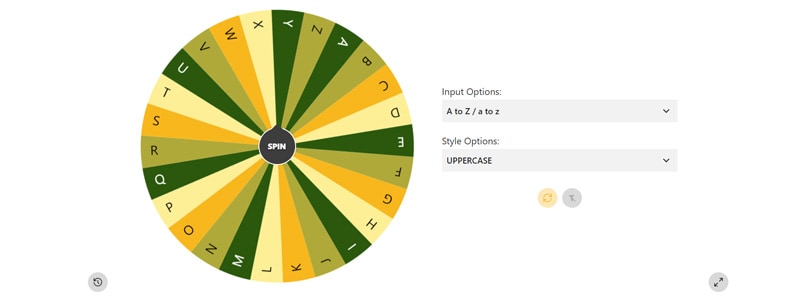
The generator is presented in the form of a Wheel of Fortune. You spin and wait for a random letter of the English alphabet to drop out. The number of attempts is unlimited. Thanks to the game form, the process is fun and easy.
To get the result, click on “Rotate.” If you scroll down the page, you will see the settings. In them, you can change the speed and duration of the wheel rotation. You can select letter sizes and style options. Check the “Stop manually” checkbox and control the whole process yourself. Free from annoying pop-ups.
Random org
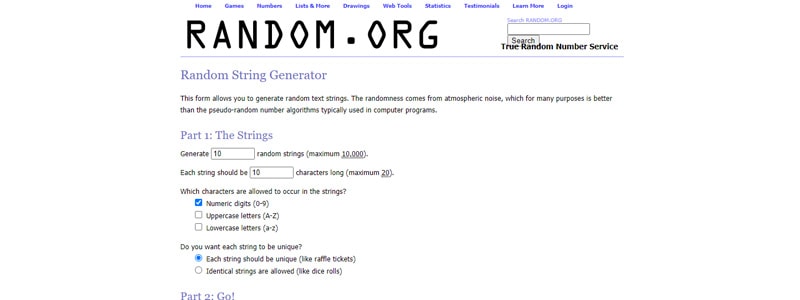
Another random generator greets visitors with a reflection on the spontaneity of the world in general. In addition letters, it offers generating whatever you want. For example, countless lines are unique, like lottery tickets. But no more than 10,000 at a time. Or a kaleidoscope of random drawings. Based on measured and chaotically changing parameters – thermal and shot noise, photoelectric effect, and quantum phenomena. Don’t ask what it is – follow the link and study the generator yourself.
The program has a simple and user-friendly interface. There is a list of paid and free services. The price of a subscription or one-time payment can be calculated using the cost calculator. Another plus is the complete absence of advertising.
The word counter

This random letter generator is a great tool for solving tons of problems. It works quickly and easily. The case contains the alphabets of ten languages, including oriental ones. To get the result, you just need to:
- Enter the number of letters in the field.
- Select the desired language.
- Press the “Generate random letter” button.
In addition, random words can be generated. In addition, the service has a section “Grammar Tips” with a spell checker and a thematic blog.
The interface is very simple – anyone can use the generator, regardless of age or computer skills. Free. Advertising, respectively, is present.
Giga calculator
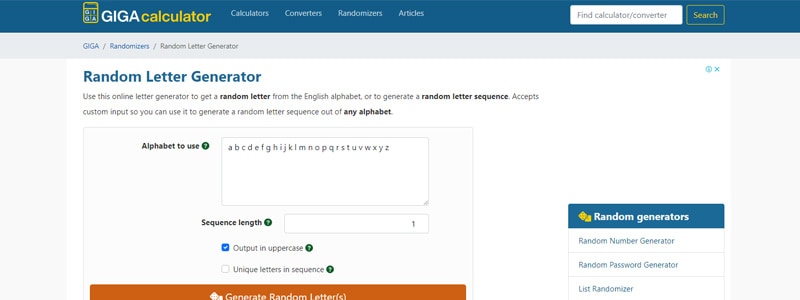
In addition to generating letters, passwords, names, countries, colors, and God knows what else. The service offers to choose a tool for solving everyday tasks. The site contains financial and household calculators:
- Percentage
- Loans
- Biological age
- BMI
- VAT
- Others
There are also online converters – mathematical and physical converters.
Interesting, helpful, and free. And it is very convenient to use – your grandmother would be able to cope with the task. The downside is the distracting ads.
As a result
Using free generators in business and life is a great idea. With their help, you can “close” many routine and boring tasks. And if you add a little creativity, you get an addictive and rewarding game. So take advantage of our tips, and generate at your pleasure.
